Hans Fuller – March 2015
We were struggling with a very common problem; users inadvertently move files and folders by accident. Then all of a sudden the files are gone and we need to use our shadow copy or restores to get the data back. There has to be a way to control this with simple file permissions.
I have looked at this before and was not able to figure it out. On the internet there does not seem to be a straight forward answer. There must be a way to set up a folder structure so the users can create and delete files but they can not move, modify or delete the folders. Also, I want this to work without having to modify each folder individually, so the permissions need to inherit.
So here is the solution that I have come up with.
These points helped me figure out how to make this work.
- Multiple permissions entries can be made to the same group or users for the same object.
- Permissions are cumulative, start with the minimum required permissions and then add permissions required further down the folder structure.
- Any Folder and also file Creation permissions need to be managed from the parent folder not the actual folder you want to control.
- This was the big one, once I figured this out it all made sense Separate Permissions can be applied to only affect Files and Folders etc.
- The Delete permission works for the individual Files
- The Delete Subfolders and Files permission is controlled from the parent folder, depending how you apply it you can apply it to Folders, Files or both
**Note, Full Permission bypasses everything. Turn it off
I want to set up my structure so that users have read access and by simply adding one entry somewhere in the folder tree I will allow a file delete/modify. These permissions should then propagate to all the child folders. I also want to easily be able to control file and directory permissions separately to stop users from moving or deleting folders and files by accident.
Below are three different scenarios and how we can achieve this. It seems pretty simple.
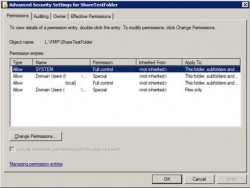
For my examples I used the Domain User account and created the structure as an administrative account with full permissions. Inheritance is turned off on the root level folder and then turned on for all the sub folders. We are working in the advanced security tab.
Try it out and play with it a bit. This should be enough to get you going and understand the concept.
Disable Folder Moves, Deletion and Creation of folders
We add 2 separate permissions sets on the parent folder
- Add First permission set check for Domain User
Un-Check Full Control, Delete Subfolder and Files and Delete
These permissions need to apply to Folders, Subfolders and Files - Add Second permission set check for Domain User
Only the Delete Permission is checked
This permission needs to apply to Files only
With an administrative login then go ahead and create sub-folders.
Then log in with a non administrator account and test out the result. You will able to create files but not do anything with the folder structure.
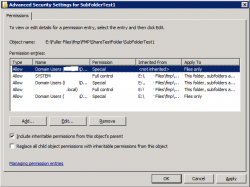
Disable Folders and top level file creation
Say you want to also control the creation of files in your top level folder.
- Same as the previous case
- Un-Check the Create Files permission
- On the sub folders add one more permission that applies to file only
- Check the Create Files permission only.
Now the users can not create files in the top level folders but can create and modify any files in the sub folders.
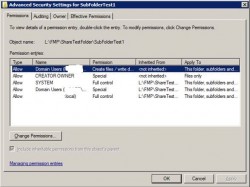
Control file delete by creator only
We may also want to ensure that users can only delete the files they create and not any other users’ files. For this case we have to make a small change to the parent and child folder.
- Start as in case 2 but two changes
- Remove the security entry that has the delete only permission on the parent folder
- Add an entry to the File Owner and check off only the delete permission on the child folder
For this case the users should now be able to add files but not delete or modify any files not created by them.
You can further change the functionality by possibly adding a modify privilege to the Domain User group permission. Now the user can create files, delete their own files but not delete other users files.
Conclusion and other points
I think by now you may get the idea how this works.
The idea is leave things un-checked and add permissions as you need and folder permissions always flow from the parent not the current folder.
As a default when I added permissions for other groups I always left all the stuff checked off. However really would it not make more sense to just check what you want Extra permission you want his though to have. If you set up the Domain user to have full read permissions then then why not just select what else the group can do.
Good luck